How do device certificates work

Nathan Sanders
Published Apr 23, 2026
A device certificate is an electronic document that is embedded into a hardware device and can last for the life of the device. The certificate’s purpose is similar to that of a driver’s license or passport: it provides proof of the device’s identity and, by extension, the identity of the device owner.
How do computer certificates work?
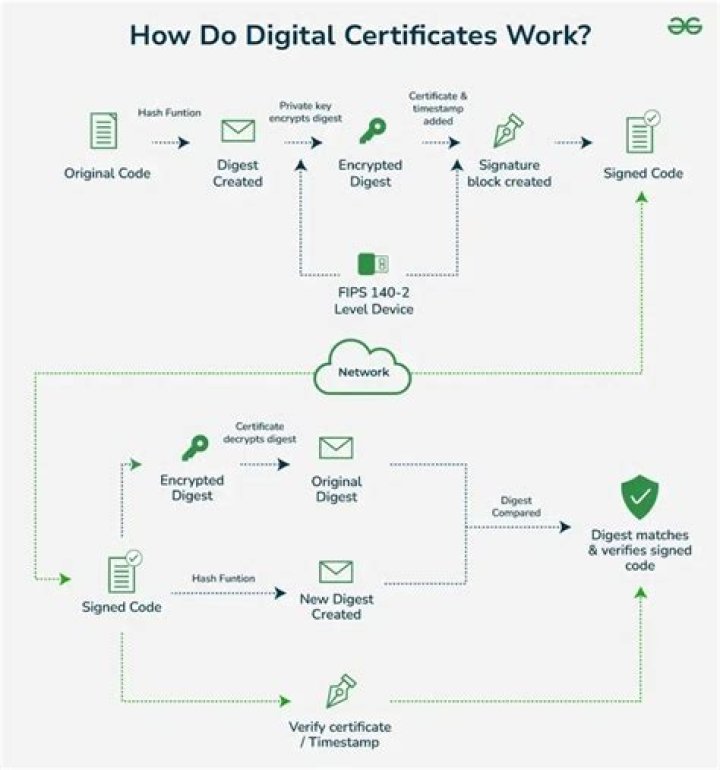
The certificate is signed by the Issuing Certificate authority, and this it what guarantees the keys. Now when someone wants your public keys, you send them the certificate, they verify the signature on the certificate, and if it verifies, then they can trust your keys.
How does certificate verification work?
To verify a certificate, a browser will obtain a sequence of certificates, each one having signed the next certificate in the sequence, connecting the signing CA’s root to the server’s certificate. … The path’s root is called a trust anchor and the server’s certificate is called the leaf or end entity certificate.
How does device based authentication work?
Endpoint authentication is a security mechanism designed to ensure that only authorized devices can connect to a given network, site or service. The approach is also known as device authentication. … The password response sent from the registered device verifies that the user is connecting from an authorized endpoint.What are certificates on phones?
Digital certificates identify computers, phones, and apps for security. Just like you’d use your driver’s license to show that you can legally drive, a digital certificate identifies your phone and confirms that it should be able to access something. Important: You’re using an older Android version.
Do I need security certificates on my phone?
Android uses certificates with a public key infrastructure for enhanced security on mobile devices. Organizations may use credentials to verify users’ identity when attempting to access secure data or networks. Organization members often must obtain these credentials from their system administrators.
How do certificates work for dummies?
The SSL certificates work using the Public Key Infrastructure (PKI) technology. This cryptography technique uses two keys, viz. a private key and a public key, that helps to encrypt the communication taking place between the two systems. … When the server receives the message, it decrypts it using the private key.
How do WiFi certificates work?
WiFi Certificate protects the registration process and encrypts log-in credentials when connecting to public WiFi, ultimately providing secure network access and increasing trust in public hotspots and sign-up services.How do network certificates work?
The web server sends the browser/server a copy of its SSL certificate. The browser/server checks to see whether or not it trusts the SSL certificate. If so, it sends a message to the web server. The web server sends back a digitally signed acknowledgement to start an SSL encrypted session.
Why do websites use digital certificates?A Digital Certificate is used to encrypt online data/information communications between an end-users browser and a website. After verifying that a company owns a website, the certificate authority will sign their certificate so it is trusted by internet browsers.
Article first time published onWhy is certificate not trusted?
The most common cause of a “certificate not trusted” error is that the certificate installation was not properly completed on the server (or servers) hosting the site. Use our SSL Certificate tester to check for this issue. In the tester, an incomplete installation shows one certificate file and a broken red chain.
How are digital certificates verified?
Digital certificates are issued by trusted parties, called certificate authorities, to verify the identity of an entity, such as a client or server. … The CA checks your signature using your public key and performs some level of verification of your identity (this varies with different CAs).
How do I know if a certificate is real?
Genuine degrees are embossed and have a gold seal and if you bring the certificate against a bright light, there should be a hologram watermark visible. The signature should also not be printed, as genuine certificates have signatures which are written in ink and they do not contain any spelling mistakes.
What happens if I clear all credentials on my phone?
Removing all credentials will delete both the certificate you installed and those added by your device. Go to your device Settings. In Settings, navigate to Security and Location. … Click on trusted credentials to view device-installed certificates and user credentials to see those installed by you.
What is the purpose of a device certificate?
A device certificate is an electronic document that is embedded into a hardware device and can last for the life of the device. The certificate’s purpose is similar to that of a driver’s license or passport: it provides proof of the device’s identity and, by extension, the identity of the device owner.
Should I disable trusted credentials?
You should not disable trusted credentials in the system tab of an Android device as doing so may lead to the phone not recognizing and establishing secure connectivity to certificates issued by a specific CA.
What does SSL stand for?
Secure Sockets Layer (SSL) is a standard security technology for establishing an encrypted link between a server and a client—typically a web server (website) and a browser, or a mail server and a mail client (e.g., Outlook).
How do you use certs?
Deploy the certificate to Chrome devices To deploy the certificate, use an open guest Wi-Fi network. Your Chrome devices will authenticate to Google and receive the TLS or SSL certificate. The pushed certificate will apply to all enrolled Chrome devices on the primary domain.
What is SSL Tutorialspoint?
Secure Socket Layer (SSL) is a security protocol that was developed by Netscape Communications Corporation, along with RSA Data Security, Inc. It has two layers which are SSL Record Protocol and SSL Handshake Protocol.
Why is my network being monitored?
Google added this network monitoring warning as part of the Android KitKat (4.4) security enhancements. This warning indicates that a device has at least one user-installed certificate, which could be used by malware to monitor encrypted network traffic.
How do I root my phone?
- Download the APK.
- Install it — you may need to tap the Unknown Sources button in your Android Security settings to complete the installation.
- Open the app, and tap Root.
- If it can root your device, you can root your device.
- You then must download and run Magisk to manage your root access.
Why does my phone have so many certificates?
To put it simply is because each of those certificates represents an authority which the phone manufacturer trusts. When you visit a website or a similar service it presents a certificate to your browser which is supposed to certify the identity of that site.
What does certificate authentication provide?
Certificate-based authentication is the use of a Digital Certificate to identify a user, machine, or device before granting access to a resource, network, application, etc. In the case of user authentication, it is often deployed in coordination with traditional methods such as username and password.
How secure is certificate-based authentication?
Certificates utilize public-private key encryption to encrypt information sent over-the-air and are authenticated with EAP-TLS, the most secure authentication protocol. A major flaw with credential-based networks can be linked to human behavior. Many people reuse passwords or use weak passwords.
How does SSL and TLS work?
SSL/TLS uses both asymmetric and symmetric encryption to protect the confidentiality and integrity of data-in-transit. Asymmetric encryption is used to establish a secure session between a client and a server, and symmetric encryption is used to exchange data within the secured session.
Is WiFi certificate safe?
Certificates provide a more secure form of network authentication than passwords because they are encrypted and locked onto devices.
Is a token a certificate?
There are a couple of major difference between a token and a certificate. Tokens are essentially a symmetric key. That means that the same key has to be both on the client and the server to be able to authenticate users. Certificates use an asymmetric set of keys.
Can digital certificates be hacked?
Many businesses view encryption as the ultimate protection. But a compromised, stolen or forged digital key and certificate can enable attackers to impersonate, surveil and monitor websites, infrastructure clouds and mobile devices.
Who uses digital certificates?
Digital certificates are used for card holders (electronic credit cards) and merchants. The use of digital certificates in SET allows for secure, private connections between card holders, merchants, and banks. The transactions created are secure and indisputable, and they cannot be forged.
What is the advantage of digital certificate?
The Advantages of Digital Certificates The biggest advantages of digital certificate-based authentication are privacy-based. By encrypting your communications — emails, logins or online banking transactions — digital certificates protect your private data and prevent the information from being seen by unintended eyes.
Where can I find untrusted certificates?
You can find some of the certificates in their GitHub repository. On Chrome, you can also export the certificate used for a tab. Click on “Not Secure”, then click on “invalid” under “Certificate”. See the details tab, then click “export” to save the certificate.