What is involved in the copying method of dumpster diving

Andrew Mitchell
Published Apr 18, 2026
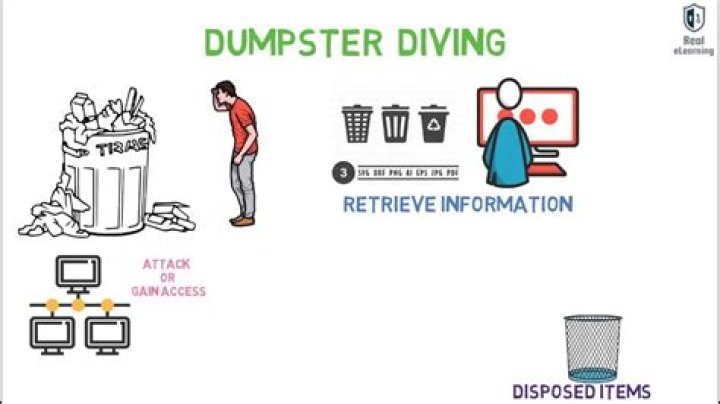
Watt is involved in the copying method of dumpster diving? The tactics are casing the physical location and discovery of schedules that allow easy access to trash or information, and then copying information and leaving the original where it was found.
What is a dumpster diving technique?
Dumpster diving is looking for treasure in someone else’s trash. In the world of information technology (IT), dumpster diving is a technique used to retrieve information that could be used to carry out an attack or gain access to a computer network from disposed items.
What type of attack is dumpster diving?
A dumpster diving attack is a type of cyber attack made possible by searching through the victim’s trash. While you might be imagining a messy and filthy scenario where a person dives into a dumpster, the reality is less unsanitary.
How is dumpster diving used as a technique in the crime of stolen identity?
Dumpster diving Thieves go through the garbage to find account numbers, Social Security Numbers, and other sensitive information from personal, financial, and medical documents. They use this information to assume or sell your financial identity.What is dumpster diving how it can be prevented?
Preventive Measures: Destroy any CDs/DVDs containing personal data. In case you no longer need your PC, make sure you have deleted all the data so that it can’t be recovered. Use of firewalls can prevent suspicious Internet users from accessing the discarded data.
How do you go dumpster diving?
- Play the numbers game. …
- Go to the source. …
- Get in and look around. …
- Manage your fear. …
- Bring the supplies you need and be prepared. …
- Focus on middle and upper income areas. …
- Go with a friend if you can. …
- Don’t let locks fool you.
What is dumpster diving and piggybacking in detail?
Piggybacking: Here the attacker may pose as an employee and ask the authorised employee to allow him to enter along with him. He may give fake reasons like he forgot his smart badge, etc. Dumpster Diving: Any confidential or sensitive document should be properly shredded before disposed into the dustbin.
What is dumpster diving quizlet?
What is dumpster diving? Going through trash and looking for people’s personal information.What is dumpster diving in social engineering?
Dumpster Diving is investigating a person or business’s trash to find information that can be used to attack a computer network. Once in hand, the information is used to piece together identity profiles, making social engineering more likely to succeed. …
How can dumpster diving prevent identity theft?- Keep Your Dumpsters Well-Lit to Discourage Diving. …
- Install Motion-Sensing Cameras Focused on Dumpsters. …
- Destroy All Documents That Contain Personal or Business Information. …
- Hire a Remote Monitoring Service to Watch Your Dumpsters.
What is the most effective tool to use against dumpster diving attacks?
To prevent dumpster divers from learning anything valuable from your trash, experts recommend that: Consumers: use a paper shredder to destroy all papers that have personal information.
Why dumpster diving is a problem?
Dumpster diving can be hazardous, due to potential exposure to biohazardous matter, broken glass, and overall unsanitary conditions that may exist in dumpsters. Arguments against garbage picking often focus on the health and cleanliness implications of people rummaging in trash.
How can dumpster diving give attackers valuable information?
How can dumpster diving give attackers valuable information? People can look in the trash for sensitive information that has not been properly disposed of. What is the best defense against a social engineering attack?
Which of the following are the best ways to protect your Organisation against revealing sensitive information to dumpster divers?
Audible Alarms So, one of the best ways to prevent it is to install an audible alarm. The alarm will detect the sounds when the noise from dumpster diving is detected and alert your security company as well as the proper authorities. Glass break detector is one of the most popular types of audible alarms.
Is dumpster diving illegal in Phoenix AZ?
Dumpster diving may be illegal in Phoenix, but that hasn’t stopped many from plunging into trash to find food or commit identity theft. … Despite being considered a misdemeanor in some Valley cities and a civil offense in others, dumpster diving attracts a variety of people with a wide range of motives.
What type of attacks are tailgating dumpster diving and shoulder surfing?
Social Engineering attacks could involve anything from Phishing and Vishing attacks to dumpster diving and shoulder surfing.
What can you find dumpster diving?
- Construction and Remodeling Sites. You can find a lot of quality stuff in construction site dumpsters. …
- Grocery Stores. …
- Retail Stores. …
- Colleges and Universities. …
- Residential Curbside Cans. …
- Apartment Complexes. …
- Florists. …
- Swap Meets.
What happens if you dumpster dive?
However, it is important to understand that, while dumpster diving is not illegal in California per se, most people arrested for dumpster diving have violated other municipal laws during the activity and can face criminal prosecution under local laws.
How does pharming affect your computer?
How does pharming work? … Pharming attacks this process in one of two ways: First, a hacker may send malicious code in an email which installs a virus or Trojan on a user’s computer. This malicious code changes the computer’s hosts file to direct traffic away from its intended target and toward a fake website instead.
What is the thesis of On Dumpster Diving?
Lars Eighners essay “On Dumpster Diving” describes the lifestyle of living out of a dumpster. Lars demonstrates that anyone can achieve a fulfilling life without the constraints of society and material wealth. He finds nearly everything he needs and sometimes more just from the refuse of others.
What three principles are required to eat safely from a dumpster?
His essay starts by uttering some guidelines of what is and is not safe to eat. “Eating safely from the dumpsters involves three principles: using common sense for evaluating the food, knowing the dumpsters of the given areas and always ask, “Why was this discarded?” (Eighner 714).
What is the effect of Lars eighner's attention?
1. Eighner’s attention to language in the first five paragraphs affects the tone of his essay. He is informative and explains to the reader that he prefers “the word scavenging and use the word scrounging,” rather than “foraging,” or “Dumpster diving” (713).
What are 5 steps one could take to protect him herself from ID theft?
- 10 Ways To Protect Yourself From Identity Theft. …
- Destroy private records and statements. …
- Secure your mail. …
- Safeguard your Social Security number. …
- Don’t leave a paper trail. …
- Never let your credit card out of your sight. …
- Know who you’re dealing with. …
- Take your name off marketers’ hit lists.
What information is most commonly stolen from social media?
- Full name (particularly your middle name)
- Date of birth (often required)
- Home town.
- Relationship status.
- School locations and graduation dates.
- Pet names.
- Other affiliations, interests and hobbies.
What is identity theft phishing?
Tricking consumers into disclosing their personal and financial data, such as secret access data or credit card or bank account numbers, is identity theft. Such schemes perpetrated through the Internet are called “phishing” for information. … Identity theft schemes take numerous forms.
What is a common method used in social engineering cyber awareness 2020?
Phishing attacks are the most common type of attacks leveraging social engineering techniques. Attackers use emails, social media, instant messaging and SMS to trick victims into providing sensitive information or visiting malicious URLs in the attempt to compromise their systems.
What is a social engineering technique?
Social engineering is the term used for a broad range of malicious activities accomplished through human interactions. It uses psychological manipulation to trick users into making security mistakes or giving away sensitive information.
How do I secure my dumpster?
- Light it Up. Place your dumpster in a well-lit area, either near existing streetlamps or with temporary lighting.
- Cover the Bin. Place a tarp over your container when no one is working.
- Fence Your Site. …
- Avoid Street Placement. …
- Post a Warning Sign. …
- Plan for Security.
Which of the following terms refers to an activity which involves criminals searching through?
Explanation: In general, Stalking refers to continuous surveillance on the target (or person) done by a group of people or by the individual person.