What is Eventstats Splunk

Ava Robinson
Published Apr 21, 2026
From Splunk documentation, “The eventstats command calculates statistics on all search results and adds the aggregation inline to each event for which it is relevant. The streamstats command calculates statistics for each event at the time the event is seen, in a streaming manner.”
What is the difference between stats and eventstats in Splunk?
The eventstats command is similar to the stats command. The difference is that with the eventstats command aggregation results are added inline to each event and added only if the aggregation is pertinent to that event.
What is Streamstats Splunk?
Splunk software provides a command named streamstats that adds all the cumulative summary statistics to all search results in a streaming or a cumulative manner. This command calculates the statistics for each event when it is observed. … The streamstats command is also similar in comparison with the stats command.
What is the difference between the stats Tstats and Eventstats search commands?
In above example stats command has returned 4 statistical results for field “log_level” with count of each value in that field. Eventstats calculates a statistical result same as stats command only difference is it does not create statistical results, it aggregates them to the original raw data.How does Splunk append work?
Append is a streaming command used to add the results of a secondary search to the results of the primary search. The results from the append command are usually appended to the bottom of the results from the primary search. After the append, you can use the table command to display the results as needed.
Why is Tstats faster?
Tstats are faster than stats, as tstats looks only at the indexed metadata, . tsidx files. (i.e., only metadata fields such as source type, host, source, and _time). The indexed fields are from normal index data, accelerated data models, or tscollect data.
What is Eventstats?
From Splunk documentation, “The eventstats command calculates statistics on all search results and adds the aggregation inline to each event for which it is relevant. The streamstats command calculates statistics for each event at the time the event is seen, in a streaming manner.”
What is Eventcount in Splunk?
The eventcount command just gives the count of events in the specified index, without any timestamp information.Which of these are splunk stats command?
- Finding Average. We can find the average value of a numeric field by using the avg() function. …
- Finding Range. The stats command can be used to display the range of the values of a numeric field by using the range function. …
- Finding Mean and Variance.
The eval command calculates an expression and puts the resulting value into a search results field. If the field name that you specify does not match a field in the output, a new field is added to the search results.
Article first time published onWhat is Mvexpand?
Expands the values in a multivalue field into separate events, one event for each value in the multivalue field.
What is coalesce in Splunk?
Coalesce is an eval function (Use the eval function to evaluate an expression, based on our events ). This function takes an arbitrary number of arguments and returns the first value that is not NULL. We can use this function with the eval command and as a part of eval expressions.
How do I sort in Splunk query?
- Specify different sort orders for each field. This example sorts the results first by the lastname field in ascending order and then by the firstname field in descending order. …
- Specify the number of sorted results to return.
How does Splunk Dedup work?
The Dedup command in Splunk removes duplicate values from the result and displays only the most recent log for a particular incident. The Splunk Dedup command will return the first key value found for that particular search keyword/field.
What is Splunk add on builder?
The Splunk Add-on Builder helps you build and validate add-ons for your Splunk platform deployment. The Splunk Add-on Builder is ideal for: Splunk admins who would like to onboard additional data into the Splunk platform. Developers who are looking for a tool to help them build and validate a Splunk add-on.
What is Append command in Splunk?
Append command appends the result of a subsearch with the current result. … It doesn’t show the correct result if you use this command in real time basis. The subsearch must be start with a generating command.
What is Tstats command?
Similar to the stats command, tstats will perform statistical queries on indexed fields in tsidx files. Significant search performance is gained when using the tstats command, however, you are limited to the fields in indexed data, tscollect data, or accelerated data models.
What is the default number of field values returned by the Fieldsummary command?
In SPL, the default number of distinct values returned for a field is 100.
What is metasearch in Splunk?
metasearch — this actually uses the base search operator in a special mode where we do not read from the journal.gz. So this is an event based command. We actually treat things as events. Due to the fact that we are not reading form the journal.gz this can only use information that exists in the tsidx files.
What is metadata in Splunk?
The metadata command is a generating command, which means it is the first command in a search. For those not fully up to speed on Splunk, there are certain fields that are written at index time. … This is a quick search that I could run to enumerate sourcetypes in Splunk for the past seven days.
What is Summariesonly in Splunk?
Splunk Employee. 10-24-2017 09:54 AM. In this search summariesonly referes to a macro which indicates (summariesonly=true) meaning only search data that has been summarized by the data model acceleration. Summarized data will be available once you’ve enabled data model acceleration for the data model Network_Traffic.
What is DC in Splunk?
12-30-2019 11:51 AM. dc is Distinct Count. It says how many unique values of the given field(s) exist.
What is top command in Splunk?
TOP allows you to easily find the most common values in fields. It will also help you find information behind your event values like count and percentage of the frequency.
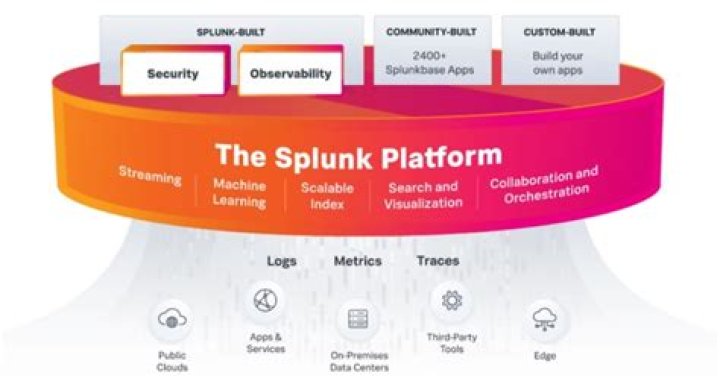
What is Splunk pipeline?
data pipeline noun. The route that data takes through Splunk Enterprise, from its origin in sources such as log files and network feeds, to its transformation into searchable events that encapsulate valuable knowledge.
What fields are available in Tstats?
- _time.
- _indextime.
- source.
- sourcetype.
- host.
- punct.
How do you use count command in Splunk?
statushostcount200www111835200www211186200www311261400www1233
What is Rex in Splunk?
Rex command in splunk is used for field extraction in the search head. This command is used to extract the fields using regular expressions. This command is also used for replacing or substitute characters or digits in the fields by the sed expression.
What is Mvindex in Splunk?
Usage of Splunk EVAL Function: MVINDEX : • This function takes two or three arguments( X,Y,Z) • X will be a multi-value field, Y is the start index and Z is the end index.
Where is syntax in Splunk?
The where command uses <predicate-expressions> to filter search results. A predicate expression, when evaluated, returns either TRUE or FALSE. The where command only returns the results that evaluate to TRUE. The where command is identical to the WHERE clause in the from command.
How do you split a Multivalue field in Splunk?
The “split” command was used to separate the values on the comma delimiter. Using mvindex and split functions, the values are now separated into one value per event and the values correspond correctly. This function can be used to quickly determine the number of values in a multivalue field using the delimiter.
How do I rename a field in Splunk?
Use the rename command to rename one or more fields. This command is useful for giving fields more meaningful names, such as Product ID instead of pid . If you want to rename fields with similar names, you can use a wildcard character.