What are three cyber security issues

Victoria Simmons
Published Apr 21, 2026
Adapting to a Remote Workforce. It’s no secret that there’s been a significant increase in the number of people working remotely. … Emerging 5G Applications. … Blockchain and Cryptocurrency Attacks. … Internet of Things (IoT) Attacks. … Phishing Scams.
What are 3 challenges of cyber security?
- Adapting to a Remote Workforce. It’s no secret that there’s been a significant increase in the number of people working remotely. …
- Emerging 5G Applications. …
- Blockchain and Cryptocurrency Attacks. …
- Internet of Things (IoT) Attacks. …
- Phishing Scams.
What are the 3 major types of cyber security?
- Cloud Security. Cloud-based data storage has become a popular option over the last decade due to its enhanced privacy. …
- Network Security. Guard your internal network against outside threats with increased network security. …
- Application Security.
What are the cyber security issues?
Besides, there are some social media cybersecurity challenges like acquiring control over the customers’ accounts, phishing various campaigns running on social platforms like Facebook, Twitter, and misuse of data which is potentially important.What are the 5 threats to cyber security?
- Phishing. Phishing is a hacking scheme that tricks users into downloading harmful messages. …
- Malware. …
- Ransomware. …
- Data Breaches. …
- Compromised Passwords.
What are the types of cyber security?
- Application Security. This is the process of protecting sensitive information at the app-level. …
- Operational Security. …
- Denial-of-Service Attacks. …
- Malware. …
- SQL Injection. …
- Man-in-the-Middle Attack. …
- Drive-By Downloads. …
- Password Attack.
What are the different types of cyber threats?
- Malware. Malware is a term used to describe malicious software, including spyware, ransomware, viruses, and worms. …
- Phishing. …
- Man-in-the-middle attack. …
- Denial-of-service attack. …
- SQL injection. …
- Zero-day exploit. …
- DNS Tunneling.
What are the top cyber security threats?
- Ransomware & Malware. …
- Endpoint Attacks. …
- Phishing. …
- Third-Party and Supply Chain Attacks. …
- Machine Learning and Artificial Intelligence Attacks. …
- IoT Attacks. …
- Inadequate Patch Management. …
- Formjacking.
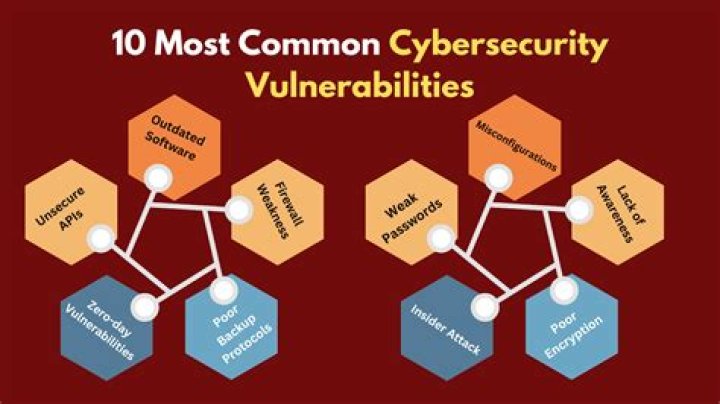
What are the most common cyber security threats?
- 1 – Malware. We’ll start with the most prolific and common form of security threat: malware. …
- 2 – Password Theft. …
- 3 – Traffic Interception. …
- 4 – Phishing Attacks. …
- 5 – DDoS. …
- 6 – Cross Site Attack. …
- 7 – Zero-Day Exploits. …
- 8 – SQL Injection.
- Critical Infrastructure Cybersecurity. The critical infrastructure cybersecurity technique is deployed to secure the systems that have the critical infrastructure. …
- Network Security. …
- Cloud Security. …
- Internet of Things Security. …
- Application Security.
What are the three threat sources?
Threats to control systems can come from numerous sources, including hostile governments, terrorist groups, disgruntled employees, and malicious intruders.
What are the four types of cyber attacks?
- Malware. The term “malware” encompasses various types of attacks including spyware, viruses, and worms. …
- Phishing. …
- Man-in-the-Middle (MitM) Attacks. …
- Denial-of-Service (DOS) Attack. …
- SQL Injections. …
- Zero-day Exploit. …
- Password Attack. …
- Cross-site Scripting.
What is cyber security?
Cyber security is the application of technologies, processes and controls to protect systems, networks, programs, devices and data from cyber attacks. It aims to reduce the risk of cyber attacks and protect against the unauthorised exploitation of systems, networks and technologies.
What are the latest cyber threats?
- Threat Profile: SmokeLoader. High.
- Threat Profile: Zloader. High.
- Log4Shell – A Log4j Vulnerability – CVE-2021-44228. High.
- Threat Profile: Remcos RAT. High.
- Threat Profile: BlackCat. High.
- PseudoManuscrypt Spyware Attack Campaign. …
- Threat Profile: Agent Tesla. …
- Blister Malware Campaign Uncovered.
What is CIA cyber security?
Confidentiality, integrity and availability, also known as the CIA triad, is a model designed to guide policies for information security within an organization. The model is also sometimes referred to as the AIC triad (availability, integrity and confidentiality) to avoid confusion with the Central Intelligence Agency.
Why is Cyber Security?
Cyber security is important because it encompasses everything that relates to protecting our data from cyber attackers who want to steal this information and use it to cause harm. … If these systems, networks, and infrastructures don’t have the right protection in place, our data might fall into the wrong hands.
What are types of threats?
Threats can be classified into four different categories; direct, indirect, veiled, conditional. A direct threat identifies a specific target and is delivered in a straightforward, clear, and explicit manner.
What are the most important IT security issues facing companies today?
- Phishing Attacks.
- Malware Attacks.
- Ransomware.
- Weak Passwords.
- Insider Threats.